Which cyber crisis scenarios should you prioritize?
Which cyber crisis scenarios should you prioritize?
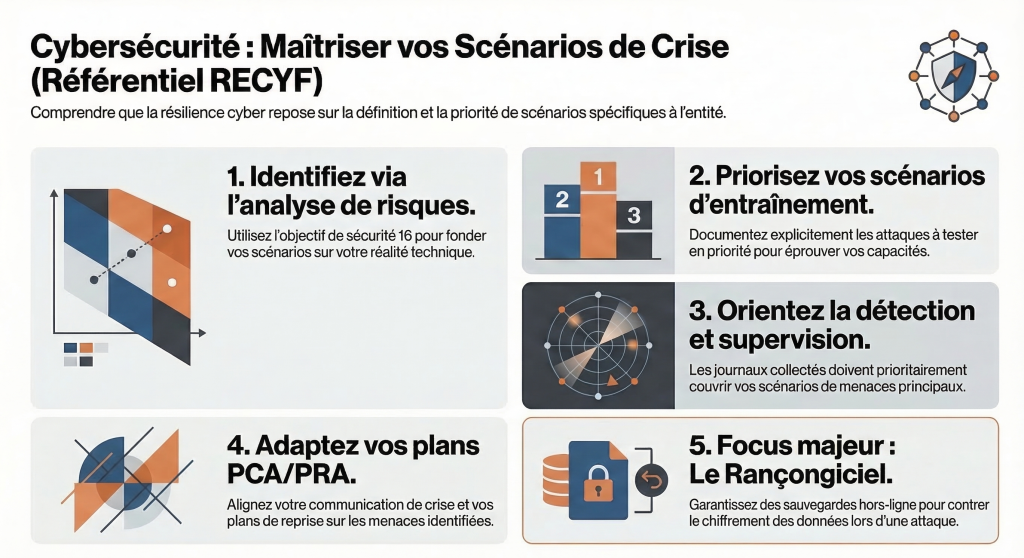
Here is the approach recommended by the RECYF framework regarding crisis scenarios:
- Identification through risk analysis: Cyber threat scenarios must be identified during the risk analysis that the entity is required to carry out.
- Defining priorities for training: As part of its training and preparedness strategy, the entity must explicitly document “the risk or attack scenarios to be tested as a priority” in order to stress-test its operational capabilities.
- : The logs and security events collected by the entity must be useful for detecting the main threat scenarios. The continuous improvement approach for monitoring should aim to optimize coverage of these identified scenarios.
- Adapting plans and communications: The crisis communication strategy, as well as the business continuity and recovery plans (BCP/DRP), must necessarily take into account the previously identified cyber threat scenarios.
While it does not impose a specific scenario, the document highlights the ransomware-type incident by citing it systematically as an example. This major scenario requires the implementation of specific protective measures — such as offline storage — to ensure that backups or technical incident records cannot be rendered unusable or encrypted by the attacker during a crisis.
Interested and looking for more information?
We take some time to discuss and listen to you.
Contact us
